Introduction to cyber security: stay safe online: Introduction to cyber security: 2.3 - OpenLearn - Open University
Legislation in ICT. Data Protection Act (1998) What is the Data Protection Act (1998) and why was it created? What are the eight principles of the Data. - ppt download

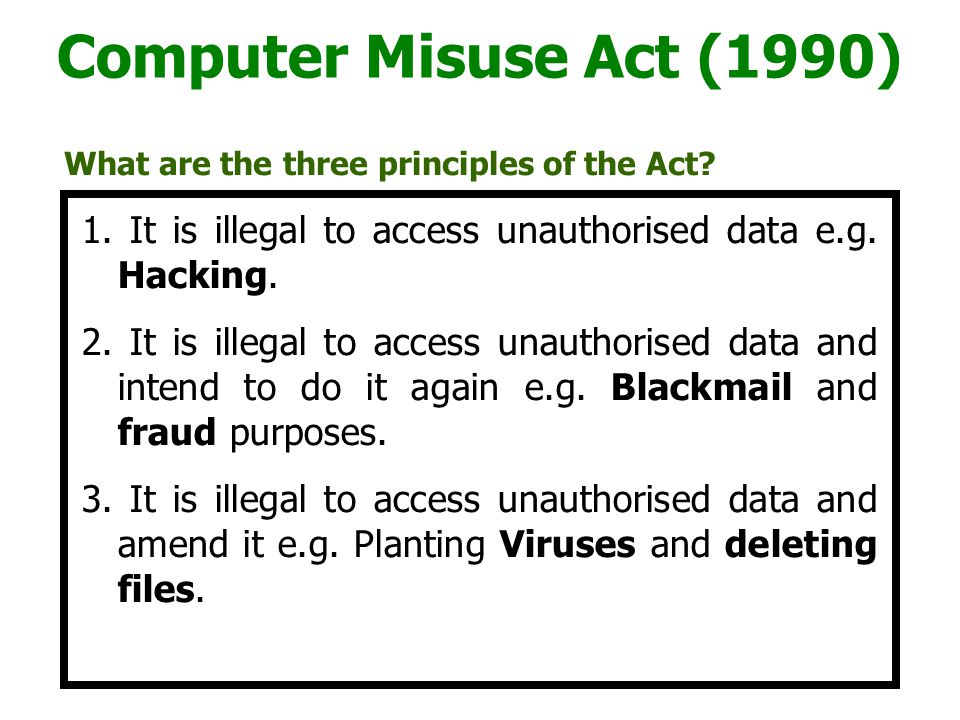
BTEC ICT Legal Issues Data Protection Act (1998) Computer Misuse Act (1990) Freedom of Information Act (2000) - ppt download